Cybercrime: More Than a Threat, an Industry
IT support in Atlanta regularly advocates IT security featuring two-factor authentication for a number of reasons, not least of which is the increasingly prevalent impact of cybercriminal enterprise. As it turns out, it is projected that by 2021, cybercrime will have a $6 trillion impact worldwide. That’s not a couple of basement dwellers who learned how to hack code and cost businesses money. That’s a concerted effort with the kind of funding which silhouettes Silicon Valley startups. There is a reason ransomware, spyware, adware, malware, social engineering hacks, and continuously developing tactics have come to define the cybercriminal market.
Complicating the issue is remote operations. As it turns out, through cloud computing which facilitates DaaS (Desktop as a Service) and BYOD (Bring Your Own Device), even small businesses can save $100k+ annually with relative ease and little complication in transition. The “other shoe” or “catch,” if you will, comes in terms of security. When facilitating a remote operational paradigm, it is absolutely essential to have the right kind of security. Competitive business requires practically every operational advantage that can be sourced. When hundreds of thousands can be cut through the cloud and BYOD, that becomes less optional than it does integral. Granted, there are advantages but without security all that can be swept away on the cybercrime winds.
IT support in Atlanta often advises IT security solutions like two-factor authentication for exactly these reasons. Advantages include:
- Exceptional increase in security via multiple areas of verification
- Facilitation of securely cost-effective development
- Updated authentication solutions going into 2018 and beyond
Looking Closer
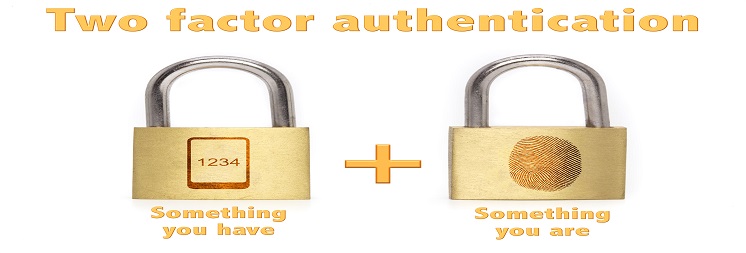
Two-factor authentication is a condensation of the concept. Multi-factor authentication is, in many ways, a more accurate description of this innovation. It’s possible for you to have multiple verification techniques. Think of it like this. In most of the blockbuster spy films, secret agencies have a thumbprint, a retina scan, a code word, and some sort of vocal examination to determine whether a person is who they say they are or not. It seems like overkill in the movies, but it’s actually sort of beneath reality.
Someone with the right software could befuddle such automatic systems. When it comes to your business, that happens all the time. Two-factor authentication is like a code being sent to a smartphone when an employee requests access to your cloud-floated DaaS. Another authentication protocol might be a remote MSP monitoring access; such that individuals are additionally contacted before they’re approved. A cybercriminal can “spoof” a phone number. It’s possible two factors may not be enough. That said, going into 2018, you’re going to need any security advantage you can source. When you’ve got multi-factor authentication, you can more cost-effectively conduct operations with security retaining its relationship with you.
Reliable Operations
IT support in Atlanta through MIS Solutions will help you facilitate more cost-effective operational solutions securely. We will, also, maintain competitiveness and increase profit while curtailing unnecessary (and arguably antiquated) infrastructural losses. Contact us for the latest in multi-factor authentication, as well as other security measures like monitoring, backup, and support. 2018 brings increased cybercriminal threats, making two-factor authentication wise.