Georgia’s healthcare data breach crisis: how 106 breaches exposed 33 million patient records in five years
How safe is your healthcare data in Georgia? We analyzed every breach reported to the federal government by Georgia healthcare organizations over the last five years to find out. The answer is sobering.
Using data from the U.S. Department of Health and Human Services Office for Civil Rights Breach Portal, we examined 106 reported breaches between 2021 and 2025. What we found challenges several common assumptions about where healthcare data is most at risk, who is responsible for the biggest exposures, and which parts of the state are hit hardest.
Key findings at a glance
- Georgia ranks #5 nationally for per-capita healthcare data breach impact. Breaches reported by Georgia organizations exposed records equivalent to nearly 3x the state’s entire population over five years.
- 106 breaches affected approximately 33 million individual records between 2021 and 2025.
- Hacking and IT incidents account for 88% of all breaches, up from 53% in 2019. The shift from physical theft to cyberattack is nearly complete.
- Business associates and health plans — not hospitals — are behind 87% of exposure. These third-party vendors report just 37% of incidents but account for the overwhelming majority of affected individuals.
- Rural Georgia counties are hit harder than metro Atlanta on a per-capita basis, with a breach rate more than 3x higher outside the metro area.
The problem is accelerating
Since 2010, healthcare organizations operating in Georgia have reported 219 data breaches to the HHS Office for Civil Rights, affecting a cumulative 38 million individual records. The pace has accelerated sharply: the last five years account for 86% of that total.
Two dynamics are driving the acceleration. First, the number of breaches has risen from an average of 9 per year in 2015–2019 to 21 per year in 2021–2025. Second, individual breaches have become far more damaging. The median breach in recent years affected more than 18,000 individuals, and several single incidents each exposed over a million records.
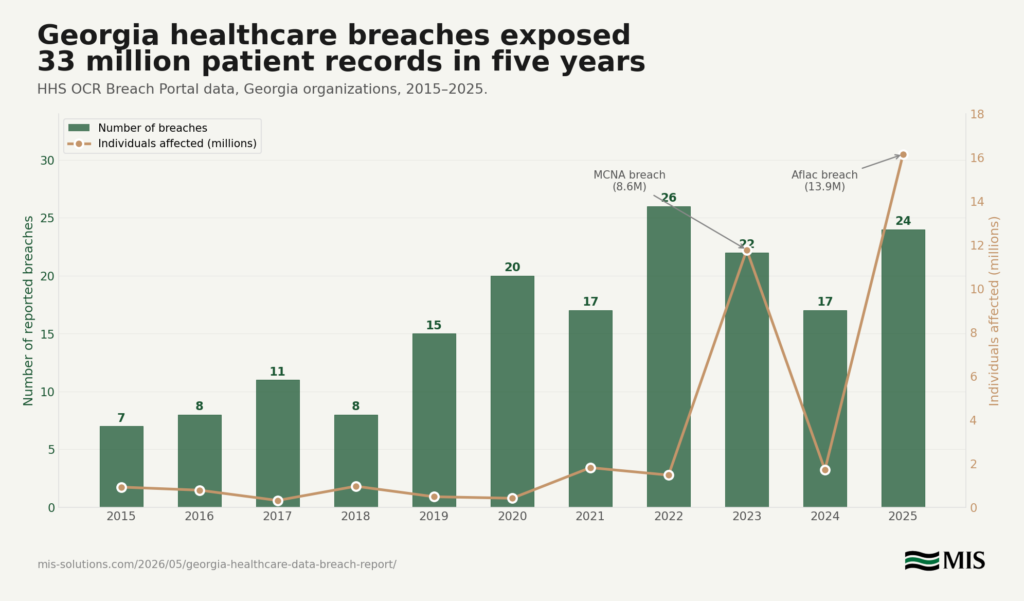
Figure 1 — Year-over-year trend chart showing breaches and individuals affected, 2015–2025
The spikes in 2023 and 2025 are largely attributable to single catastrophic incidents: the Managed Care of North America breach (8.6 million individuals in 2023) and the Aflac breach (13.9 million individuals in 2025). But even excluding those two events, the underlying trend shows steady growth in both breach frequency and scale.
How breaches happen: the shift from theft to hacking
The nature of healthcare data breaches in Georgia has fundamentally changed. A decade ago, breaches were often physical — stolen laptops, lost paper records, improper disposal. Today, the threat is overwhelmingly digital.
Hacking and IT incidents have risen from 53% of all Georgia healthcare breaches in 2019 to 88% in both 2024 and 2025. Network servers are the most common location of breached information (45% of all incidents), followed by email systems (23%).
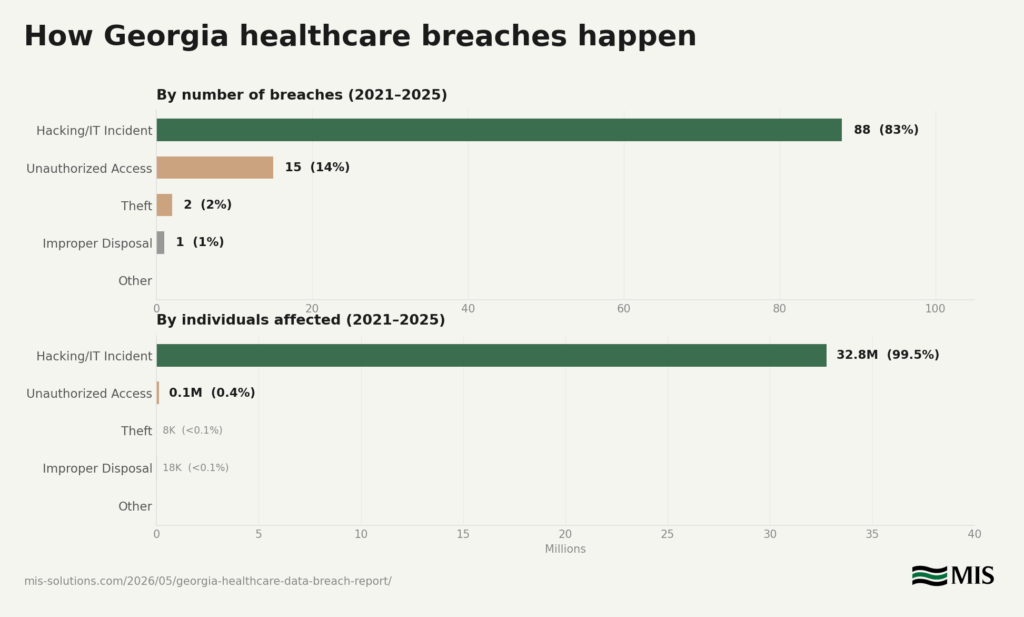
Figure 2 — Hacking percentage trend line, 2018–2025
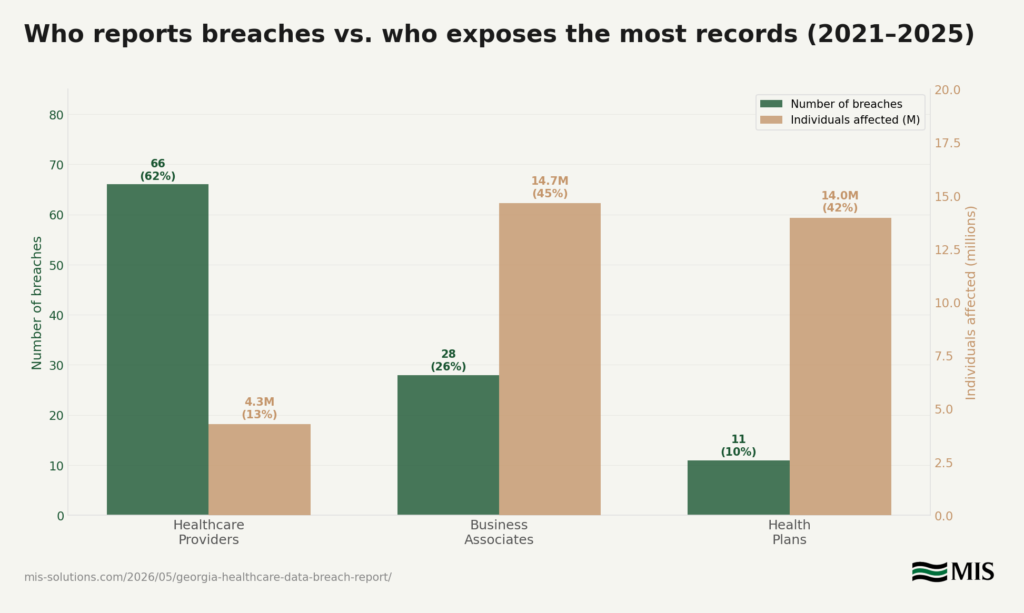
Figure 3 — Breach types by number of incidents and by individuals affected, 2021–2025
“The shift from physical theft to network-based attacks tells us something important: the organizations that haven’t modernized their cybersecurity infrastructure aren’t just behind the curve — they’re operating with open doors. Firewalls, endpoint protection, and network monitoring aren’t optional anymore. They’re the baseline.”
— Lliam Holmes, CEO, MIS Solutions
The hidden weak link: it’s not the hospital
One of the most striking findings in this analysis is the disconnect between who reports breaches and who exposes the most records.
Healthcare providers — hospitals, clinics, physician practices — account for 62% of all breach incidents over the last five years. But they account for only 13% of all individuals affected.
The vast majority of exposed records — 87% — come from business associates and health plans. These are the billing companies, claims processors, insurance administrators, and technology contractors that handle healthcare data behind the scenes. A single business associate breach can expose millions of records because these entities process data for dozens or hundreds of healthcare organizations simultaneously.
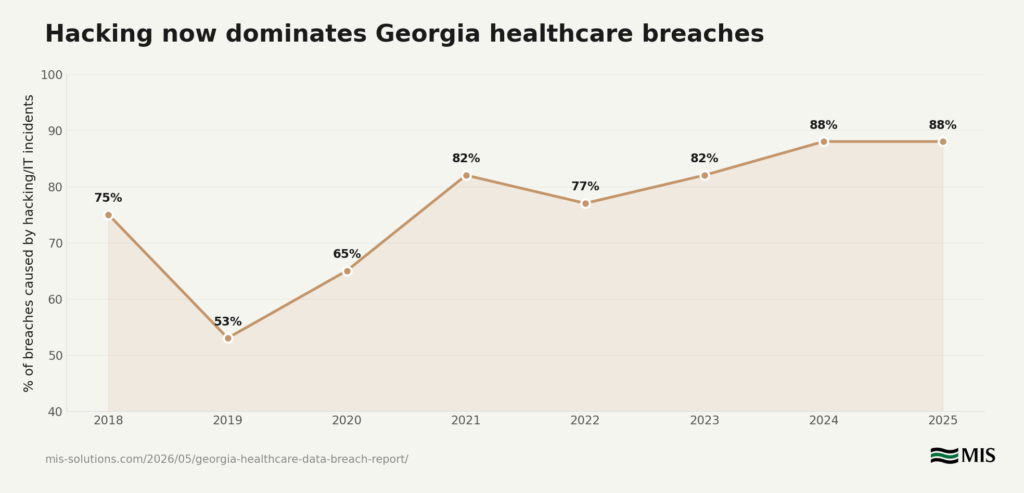
Figure 4 — Entity type comparison chart
The five largest Georgia healthcare breaches (2021–2025)
| Organization | Entity type | Individuals affected | Year |
| Aflac Incorporated | Health Plan | 13,924,906 | 2025 |
| Managed Care of North America | Business Associate | 8,627,242 | 2023 |
| NASCO | Business Associate | 1,744,655 | 2023 |
| St. Joseph’s/Candler Health System | Healthcare Provider | 1,400,000 | 2021 |
| Lockton Companies (Southeast) | Business Associate | 1,124,727 | 2025 |
Of the five largest breaches, only one was a healthcare provider. The other four were business associates or health plans.
“When a healthcare practice evaluates its cybersecurity, they typically think about their own network, their own staff, their own systems. But the data tells a different story. The biggest exposures are happening at the companies they share data with — the billing services, the claims processors, the cloud vendors. If you’re not asking hard questions about your business associates’ security posture, you’re ignoring where 87% of the damage actually occurs.”
— Lliam Holmes, CEO, MIS Solutions
Which Georgia counties are hit hardest
To understand the geographic distribution of healthcare breaches across the state, we mapped each incident to the county where the reporting organization is located. This mapping covers 73% of all affected individuals; the remaining 27% are attributable to statewide government entities or national companies that filed under Georgia in the federal portal.
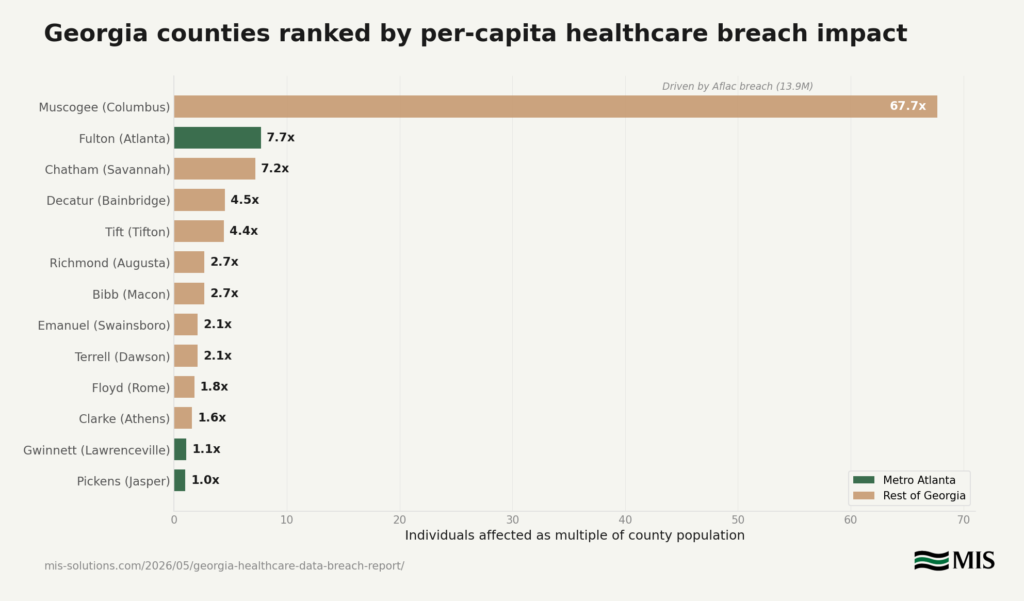
Figure 5 — County per-capita ranking horizontal bar chart
Fulton County (Atlanta) leads the state in total breach count with 90 reported incidents, reflecting its concentration of healthcare organizations. But the per-capita picture reveals a more nuanced story. Multiple counties outside metro Atlanta — including Chatham (Savannah), Tift (Tifton), Decatur (Bainbridge), and Richmond (Augusta) — have per-capita breach rates that rival or exceed the Atlanta metro area.
Top 10 Georgia counties by per-capita healthcare breach impact
| County | City | Breaches | Individuals affected | Per capita |
| Muscogee | Columbus | 12 | 14,004,818 | 67.7x* |
| Fulton | Atlanta | 90 | 8,213,801 | 7.7x |
| Chatham | Savannah | 11 | 2,133,957 | 7.2x |
| Decatur | Bainbridge | 1 | 120,085 | 4.5x |
| Tift | Tifton | 2 | 181,187 | 4.4x |
| Richmond | Augusta | 8 | 553,936 | 2.7x |
| Bibb | Macon | 3 | 408,483 | 2.7x |
| Emanuel | Swainsboro | 2 | 47,973 | 2.1x |
| Terrell | Dawson | 1 | 18,000 | 2.1x |
| Floyd | Rome | 2 | 177,968 | 1.8x |
* Muscogee County’s extreme ratio is driven primarily by the Aflac breach (13.9M individuals). Aflac is headquartered in Columbus but serves customers nationally.
Metro Atlanta vs. the rest of Georgia
Aggregating the data reveals a counterintuitive pattern: healthcare organizations outside metro Atlanta have a higher per-capita breach impact (7.7x population) than those within it (2.3x). This challenges the assumption that cybercrime is primarily an urban problem. Rural and smaller-city healthcare organizations in Georgia are experiencing significant data exposure — potentially because they have fewer dedicated IT and cybersecurity resources.
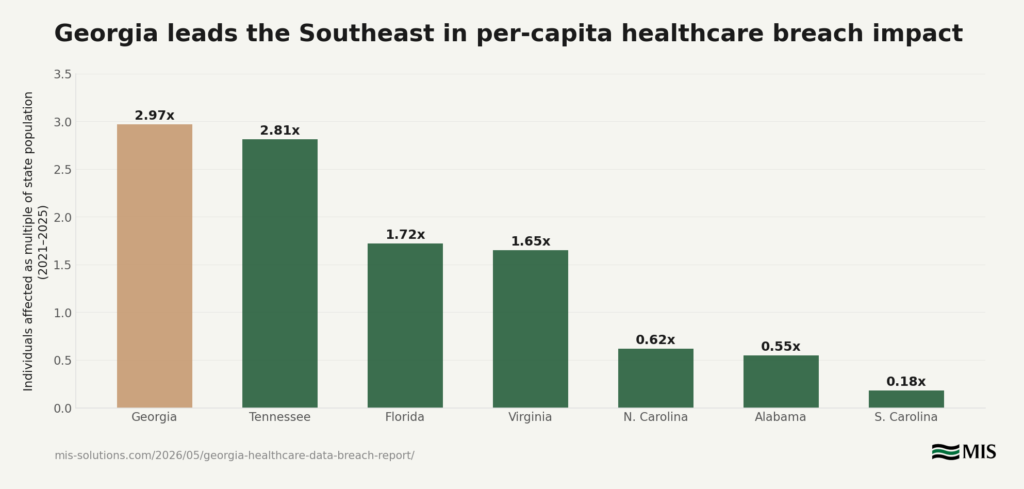
Figure 6 — Georgia vs. Southeast states bar chart
Across the Southeastern United States, Georgia ranks first for per-capita healthcare breach impact at 2.97x its population, ahead of Tennessee (2.81x), Florida (1.72x), and Virginia (1.65x). Nationally, Georgia ranks 5th — behind only Minnesota, Colorado, Delaware, and Nevada.
“There’s a misconception that cybersecurity is only a big-city problem. Our analysis shows the opposite — healthcare organizations in smaller Georgia communities are being hit hard, and they often don’t have the in-house IT teams to detect or respond to these incidents effectively. That’s the gap that managed IT services are designed to fill.”
— Lliam Holmes, CEO, MIS Solutions
What this means for Georgia healthcare organizations
The data points to three areas that healthcare organizations in Georgia should evaluate immediately:
- Audit your business associates. The biggest data exposures aren’t happening inside your organization — they’re happening at your vendors. Review your business associate agreements, ask about their security certifications, and verify that they maintain current cybersecurity controls. If a vendor can’t demonstrate SOC 2 compliance or equivalent, that’s a risk worth understanding.
- Assume hacking, not theft, is your primary threat vector. Locking filing cabinets and encrypting laptops are no longer sufficient. Network server protection, email security, endpoint monitoring, and incident response planning need to be in place. The data shows that 88% of recent breaches come through digital channels.
- Smaller organizations are not exempt. The per-capita data shows that rural and smaller-city healthcare organizations are disproportionately affected. Limited IT budgets and small teams do not make an organization invisible to attackers — they make it a softer target. Outsourcing cybersecurity monitoring and management to a qualified provider can close the resource gap without the cost of building an internal security team.
Methodology
Data source: U.S. Department of Health and Human Services, Office for Civil Rights Breach Portal (ocrportal.hhs.gov). Under the HIPAA Breach Notification Rule, covered entities and business associates must report breaches of unsecured protected health information affecting 500 or more individuals.
Scope: All HIPAA breach reports filed under the state of Georgia, including both cases currently under investigation and archived cases. The data spans April 2010 through February 2026. A total of 219 breach records were analyzed.
Per-capita calculations: Population data from U.S. Census Bureau 2024 estimates. Per-capita figures represent total individuals affected divided by the relevant population. These figures are illustrative — they do not mean every resident was personally affected.
County mapping: Each reporting entity was mapped to its primary Georgia county based on publicly available address information. National companies that filed under Georgia are categorized separately.
Important limitations
- Reporting state vs. affected population. The HHS portal lists breaches by the state of the reporting entity, not by where affected individuals reside. Organizations like Aflac serve customers nationally. The “individuals affected” figures reflect total breach scope, not Georgia-specific impact.
- Only breaches affecting 500+ individuals are included. Smaller breaches are reported to HHS but are not publicly listed. The true number of healthcare data security incidents in Georgia is likely higher than this dataset captures.
- This is not a breach notification database. Georgia does not require organizations to notify the Attorney General of data breaches, and there is no state-level public breach database. This study relies on federal HIPAA reporting, which covers only healthcare-related entities.
About MIS Solutions
MIS Solutions is an Atlanta-based managed IT services provider serving businesses across Georgia. We provide outsourced IT support, cybersecurity services, cloud solutions, backup and disaster recovery, IT consulting, AI consulting, and compliance-focused technology management. We work with healthcare organizations, professional services firms, and small to mid-sized businesses that require enterprise-grade IT security without the cost of a full in-house IT department.
For questions about this study, requests for additional data, or to schedule an interview, contact us at info@mis-solutions.com.